Merchant Card Services - PCI DSS

Back to Merchant Card Services Homepage
PCI DSS and UK
We have an obligation to protect sensitive financial information, such as credit card data, of the University's customers. That is what PCI DSS is about.
The payment card industry, which includes VISA, MasterCard, American Express, Discover, and JCB, has issued security standards to which all organizations that accept credit card data must comply. These standards are called Payment Card Industry Data Security Standards, or PCI DSS. These standards have placed additional responsibilities on your department in connection with the acceptance of payment cards. Without compliance, the card industry may refuse to allow you to process credit cards or issue fees and fines for noncompliance. Therefore, every UK office that accepts credit cards must become PCI DSS compliant.
Credit card breaches happen proportionately more in higher education due in part to decentralized processing systems and open networks. Departments may think of PCI DSS compliance as an Information Technology or Treasury issue, when in reality it is the responsibility of every department that accepts credit cards.
When a university implements a PCI compliance plan it not only protects itself, but also its students and employees. University Financial Services (formerly the Office of the Treasurer) has implemented a PCI compliance program to ensure UK's compliance with the PCI standards, to educate University administrators, faculty, and staff on PCI, and to assist departments in the compliance process.
This website is designed to introduce you to PCI DSS and provide guidance for your department’s compliance efforts. Thank you for educating yourself on this topic and for treating it with the respect it deserves.
Kevin Sisler, Director of Treasury and Merchant Card Services
Payment Card Industry Data Security Standards (PCI DSS) and Compliance Requirements for UK Merchant Departments
What is PCI DSS?
The Payment Card Industry Data Security Standards (PCI DSS) are data and record storage, transmission and system testing requirements designed to help ensure the safe handling of credit card information.
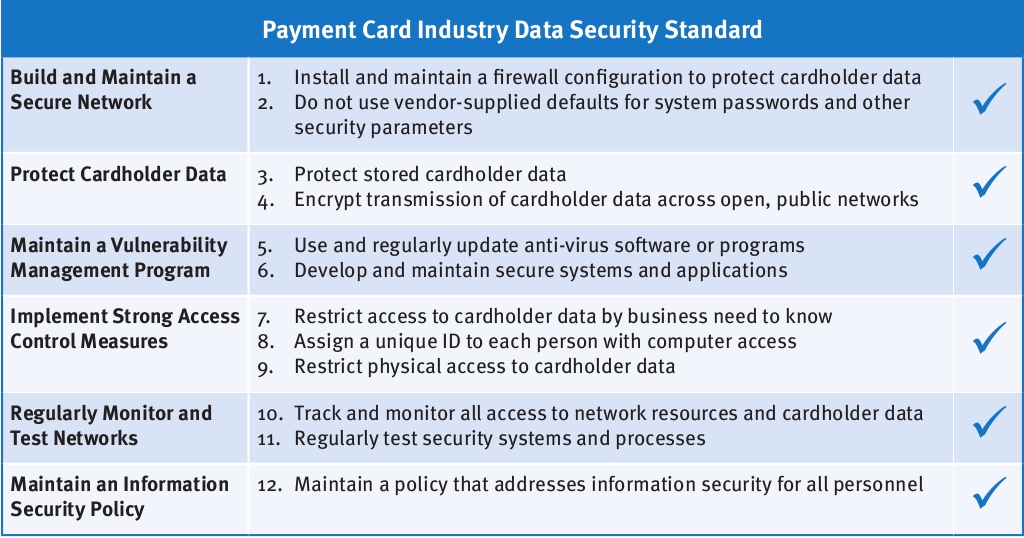
The PCI Data Security Standards are comprised of 12 general requirements.
Who sets the standards and why does UK have to comply?
The standards are set by the PCI Security Standards Council. The PCI Council was created in 2006 to align the separate security programs and standards of major card programs American Express, Discover Financial Services, JCB, MasterCard Worldwide, and Visa International. The PCI Council is led by a policy-setting Executive Committee composed of representatives from the founding credit card companies. A Board of Advisors represents the 766 participating organizations and provides feedback to the PCI Counsel.
What are Merchant Levels and why does it matter?
There are four merchant categories, “Levels”, based on the number of transactions processed. The Merchant Level designation (1, 2, 3, or 4) determines the required date of compliance and complexity and frequency of required compliance validations. The compliance requirements include, at a minimum, annual PCI Self-Assessment Questionnaires (SAQ) and quarterly network vulnerability scans. The PCI DSS SAQ is designed to evaluate data storage and security processes, to identify weaknesses if they exist, and validate a merchant’s compliance with the standards. A network vulnerability scan is a tool that remotely tests operating systems, networks and devices that could be used by hackers to target the private, secured credit card processing network. The highest level of compliance requirement is Level 1. The lowest level of compliance requirements is Level 4.
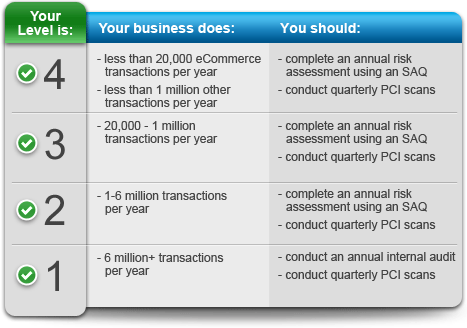
Any University units that accept credit cards for payment are consider a merchant department by UK Treasury Services, also known as Merchant Card Services (MCS). Currently, the University has more than 150 units on campus that accept credit card payments. Although these University merchant departments are separate entities processing through individual merchant accounts, our processor includes all of our merchants’ processing activity as a whole in determining the University’s overall Merchant Level for compliance validation. Based on the total combined activity of all of our merchants, UK is currently classified as a Level 3 merchant. Treasury Services deems that each merchant department is responsible for its own PCI DSS compliance and must submit to Treasury Services an SAQ, based on the merchant’s method of accepting credit card payments, to validate its compliance on an annual basis. Treasury Services will annually coordinate the SAQ completion and submission process for all University merchant departments. Additionally, Treasury Services will assist in determining which SAQ should be completed by the merchant departments and provide guidance as the merchants fill out their SAQ’s.
What are the PCI DSS Compliance requirements for University of Kentucky departments accepting credit cards (aka, Merchant Departments)?
- Develop and maintain departmental policies and procedures regarding accepting credit card payments which includes addressing the security of any credit card data handled and an incident response plan to be followed in the event of a suspected breach of that data.
- Obtain and maintain documentation of PCI DSS compliance status of any third-party service providers directly or indirectly involved in the processing of credit card transactions (e.g. website hosting services, internet payment gateways, shopping cart providers, etc.)
- Attend annual training session provided by the MCS staff of Treasury Services.
- Maintain PCI DSS compliance and complete a Self-Assessment Questionnaire (SAQ) validating compliance on an annual basis and submit to MCS of Treasury Services.
- Notify MCS of any change in credit card processing methods.
What Self-Assessment Questionnaire should the Merchant Department Complete?
https://www.pcisecuritystandards.org/documents/SAQ_InstrGuidelines_v3-1.pdf
|
A |
Card-not-present merchants (e-commerce or mail/telephone-order) that have fully outsourced all cardholder data functions to PCI DSS compliant third-party service providers, with no electronic storage, processing, or transmission of any cardholder data on the merchant’s systems or premises. Not applicable to face-to-face channels. |
|
A-EP |
E-commerce merchants who outsource all payment processing to PCI DSS validated third parties, and who have a website(s) that doesn’t directly receive cardholder data but that can impact the security of the payment transaction. No electronic storage, processing, or transmission of any cardholder data on the merchant’s systems or premises. Applicable only to e-commerce channels. |
|
B |
Merchants using only: •Imprint machines with no electronic cardholder data storage; and/or •Standalone, dial-out terminals with no electronic cardholder data storage. Not applicable to e-commerce channels. |
|
B-IP |
Merchants using only standalone, PTS-approved payment terminals with an IP connection to the payment processor, with no electronic cardholder data storage. Not applicable to e-commerce channels. |
|
C-VT |
Merchants who manually enter a single transaction at a time via a keyboard into an Internet-based virtual terminal solution that is provided and hosted by a PCI DSS validated third-party service provider. No electronic cardholder data storage. Not applicable to e-commerce channels. |
|
C |
Merchants with payment application systems connected to the Internet, no electronic cardholder data storage. Not applicable to e-commerce channels. |
|
P2PE-HW |
Merchants using only hardware payment terminals that are included in and managed via a validated, PCI SSC-listed P2PE solution, with no electronic cardholder data storage. Not applicable to e-commerce channels. |
|
D |
For Merchants: All merchants not included in descriptions for the above types. For Service Providers: All service providers defined by a payment card brand as eligible to complete a Self-Assessment Questionnaire. |
What are the costs of non-compliance with PCI DSS?
The costs of non-compliance will result primarily from a security breach if cardholder information is compromised. These costs may include:
- Notifying affected cardholders
- Paying for credit monitoring for the affected parties
- Paying for unauthorized charges
- Engaging an external Qualified Security Assessor to investigate the breach, identify vulnerabilities and produce a Report on Compliance once the vulnerabilities are mitigated
- Implementing needed hardware or software upgrades to comply with a higher level of security that would be required post-breach
- Fines from credit card companies
- Litigation from cardholders, vendors or credit card companies
- Unfavorable publicity
- Damage to UK’s reputation
The Treasury Institute for Higher Education estimates an expected cost of $182 per credit card account compromised and that a small breach (~5,000 accounts) can cost more than $1 million.
How do Credit Card Security Breaches Happen?
Types of Breaches
- Hacking into networked computers
- Lost or stolen PCs, Media (e.g. thumb drives, external hard drives, etc.)
- Improper Disposal of Records (Paper records not shredded or disposed)
- Employee theft of credit card data
- Mistakenly posting information on the Web
- Transmitting credit card data via insecure networks and systems (e.g. unencrypted Wi-Fi, email systems, etc.)
- Skimming devices on credit card processing equipment
Sources of Breaches
- Improper storing of data
- Outdated, unpatched Integrated Point of Service (POS) systems
- System logs, back-ups
- Insecure applications
- No network segmentation and/or firewalls
- Unpatched systems and/or default configuration
- Insecure wireless access points
- Use of default passwords
- No intrusion monitoring
- Unsecured Point of Sale (POS) technology
- Use of non-compliant third-party service providers
Security breaches can result in serious consequences for the University, including release of confidential information, damage to reputation, added compliance costs, substantial fines, possible legal liability and the potential loss of the ability to accept credit card payments.
Merchant departments that accept credit cards are responsible for ensuring all credit card information is received and maintained in a secure manner in accordance with PCI DSS. Individual departments will be held accountable if monetary sanctions and/or card acceptance restrictions are imposed as a result of a breach in PCI compliance.
Under no circumstance shall credit card information be obtained or transmitted via email. Credit card transactions shall not be processed or data stored on individual PCs or servers that have not been deemed PCI compliant by MCS of Treasury Services. All hard-copy credit card information must be stored in a manner that would protect the individual cardholder information from misuse, or properly destroyed if no longer needed. Remember, IF YOU DON’T NEED IT, DON’T KEEP IT.

What should a Merchant Department do if they suspect a breach of credit card information has occurred?
In the event that a merchant knows or suspects that credit card data, including card number and card holder name, has been disclosed to an unauthorized person or stolen, the Merchant Department shall immediately take the following steps.
1. The MDRP or any individual suspecting a security breach shall immediately call the Director of Treasury and Merchant Card Services.
2. The Director of Treasury and Merchant Card Services will work with the UK AT Chief Information Security Officer to determine if a breach has occurred. If an actual breach of credit card data is confirmed, MCS will alert the merchant bank, the University of Kentucky Police Department, the Legal Office, University Financial Services, the Director of Internal Audit, and any relevant regulatory agencies of the breach.
For more information on PCI DSS please visit www.pcisecuritystandards.org.
Links
- PCI DSS Self-Assessment Questionnaire
- Business Procedures (BPM) for Credit Card Merchants – See BPM E-2-1, Section VIII.
To find out if your point of sale system, processing equipment, or payment service providers are PCI DSS compliant, check these links:
- PCI SSC List of Validated Payment Applications
- VISA List of PCI DSS Compliant Service Providers
- MasterCard List of PCI DSS Compliant Service Providers
- PCI SSC List of Validated PTS Compliant Credit Card Processing Devices
Following are some useful links to learn more about the PCI DSS standards:
- PCI Security Council
- Treasury Institute for Higher Education PCI DSS Blog
- Straight Talk about Data Security, (PDF) by Walter Conway and Dennis Reedy, Business Officer, December 2007. (not valid)
- Cards at School, Why Banks View Campuses as High Risk Customers, (PDF) Dennis Reedy and Walter Conway, AEP Exchange, March 2007. (not valid)
- Walter Conway PCI DSS Guidance for Higher Education
- Boss, I think Someone Stole Our Customer Data, (PDF) Eric McNulty, Harvard Business Review, September 2007.
- The PCI Guru
- VISA
- MasterCard
- Discover
- American Express
WARNING: Some websites to which these materials provide links for the convenience of users are not managed by the University of Kentucky. The University does not review, control, or take responsibility for the contents of those sites.
